VulWall Security Certificate
What Does This Certificate Mean?
A VulWall Security Certificate confirms that an organisation's public-facing infrastructure has been automatically tested against known attack vectors, with results scored and continuously updated.
What the Assessment Covers
Every certificate is backed by automated assessments across multiple security categories.
SSL/TLS Configuration
Certificate validity, protocol versions, cipher suite strength, and HSTS enforcement.
Security Headers
Presence and configuration of headers including CSP, X-Frame-Options, and Referrer-Policy.
Known Vulnerabilities (CVEs)
Detection of exposed software versions matched against the National Vulnerability Database.
Port Exposure
Open ports and services accessible from the public internet that expand the attack surface.
Subdomain Security
Discovery and assessment of all public subdomains, including dangling DNS and misconfigured services.
Email Security
SPF, DKIM, and DMARC record validation to prevent domain spoofing and phishing attacks.
Technology Stack Analysis
Identification of frameworks, CMS platforms, and server software with known vulnerability histories.
Client-Side Dependencies
Detection of vulnerable JavaScript libraries in client-facing pages, matched against known CVE databases for frameworks like jQuery, Bootstrap, and Angular.
How the Security Score Works
The score is a weighted composite of findings across all assessment categories, normalised to a 0–100 scale. Higher-severity findings carry proportionally greater weight.
No critical or high-severity findings. Infrastructure meets strong security baselines across all assessed categories.
Some gaps found, but nothing critical. This organisation is maintaining their infrastructure.
Moderate issues present. One or more high-severity findings require remediation within a reasonable timeframe.
Significant vulnerabilities detected. Multiple high-severity or at least one critical finding is unresolved.
Severe, actively exploitable vulnerabilities present. Known exploits exist for vulnerabilities in this infrastructure. Immediate remediation needed.
Reading the Certificate
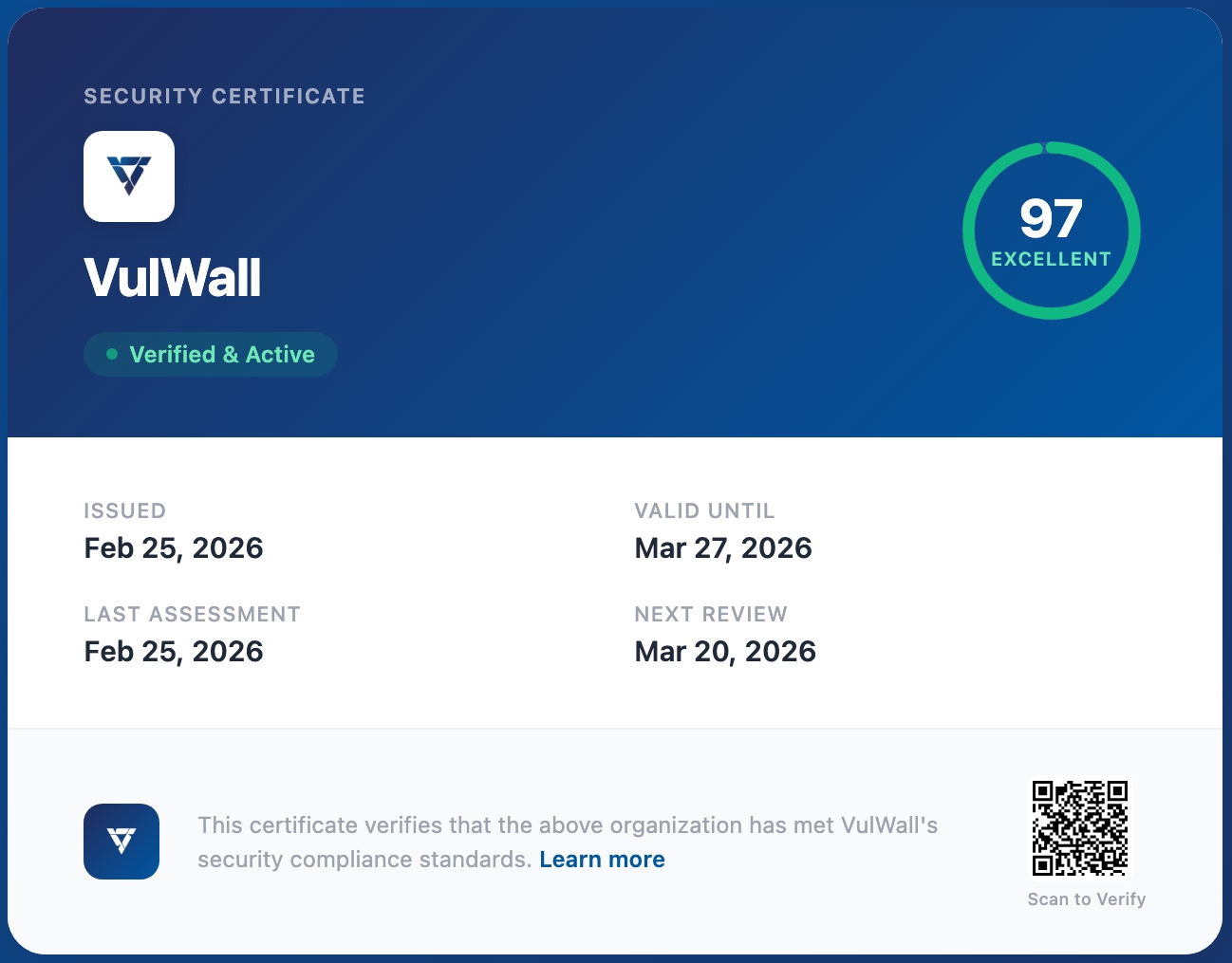
Each element of the certificate communicates a specific, verifiable claim about the assessed organisation.
Organisation Identity
The legal name and primary domain of the assessed entity. Verify this matches the organisation you are evaluating before relying on the certificate.
Security Score Ring
The overall score from the most recent assessment cycle. The ring colour corresponds directly to the tier scale described above.
Verification Status
Indicates whether the certificate is currently Active or Expired. An expired certificate means no recent assessment data is available and the score should not be treated as current.
Key Dates
Four dates provide a complete audit timeline: Issued (when the certificate was first generated), Valid Until (expiry of current assessment period), Last Assessment (most recent scan completion), and Next Review (scheduled reassessment date).
QR Code Verification
Scan to access the live certificate record directly. The QR code resolves to the authoritative VulWall record, confirming the certificate has not been altered since issuance.
Embed Badge
The badge displayed on the organisation's website reflects their current certificate status in real time. The tier shown on the badge (Excellent, Good, or Verified) corresponds directly to the security score on this certificate. If the score changes, the badge updates automatically.
Continuous Assessment
Always Current, Never Stale
Unlike point-in-time audits, a VulWall certificate is a living document.
- Assessments run on a recurring automated schedule, not on demand.
- Certificate scores reflect the results of the most recent completed assessment.
- If the organisation's security posture degrades, the score updates accordingly.
- Certificates that have lapsed are clearly marked as expired. There is no ambiguity.
Common Questions
How does this compare to SOC 2 or ISO 27001?
A VulWall certificate is complementary to, not a replacement for, SOC 2, ISO 27001, or similar compliance frameworks. Those frameworks audit internal processes, policies, and organisational controls across a broad scope. A VulWall certificate focuses specifically on the security posture of an organisation's public-facing technical infrastructure, assessed against real-world attack vectors.
The two serve different evidential purposes. An organisation holding both a SOC 2 report and a current VulWall certificate provides stronger overall assurance than either alone.
Is this the same as a penetration test?
No. A penetration test is a point-in-time, manually conducted engagement where a security professional attempts to exploit identified vulnerabilities under a defined scope. Results represent the security state at a specific moment, and findings go stale as infrastructure evolves.
VulWall assessments are automated, continuous, and focused on the measurable external attack surface. They run on a recurring schedule, meaning the certificate reflects current conditions rather than a historical snapshot. The two approaches are best understood as complementary: automated continuous coverage alongside periodic manual depth testing.
Can I rely on this for vendor due diligence?
A VulWall certificate provides a concrete, current picture of a vendor's public-facing infrastructure security posture. It is suitable as supplementary evidence in a due diligence process, particularly for assessing technical exposure, responsiveness to vulnerabilities, and the cadence of security reviews.
It does not attest to internal access controls, data handling practices, employee security training, or organisational policy compliance. For those dimensions, additional evidence such as SOC 2 reports, questionnaire responses, or contractual commitments remains appropriate.
Need a Security Certificate for Your Organisation?
If you're fielding security questions from partners, clients, or investors, VulWall can help.
Free assessment • No credit card required